In today's interconnected world, safeguarding digital assets has become paramount. Organizations across the United States face a multitude of cyber threats. To proactively mitigate these challenges, utilizing ethical hacking solutions is crucial.
Ethical hackers, also known as penetration testers, are skilled professionals who execute simulated cyberattacks to identify weaknesses in a system's security posture. By exploiting vulnerabilities before malicious actors can, they provide invaluable insights and recommendations for improving defenses.
- Nationwide ethical hacking services cater to the diverse needs of organizations of all sizes.
- These solutions often include comprehensive assessments, vulnerability scans, penetration testing reports, and tailored remediation strategies.
- Capitalizing on cutting-edge tools and techniques, ethical hackers can identify vulnerabilities in networks, applications, and infrastructure.
By investing in ethical hacking solutions, organizations can gain a competitive advantage by proactively addressing security gaps. This proactive approach helps to minimize the risk of data breaches, financial losses, and reputational damage.
California's Top-Rated Ethical Hacker For Hire
Are you afraid about the protection of your online assets? Look no further than the Central Valley's top-rated ethical hacker, ready to scan your systems and reveal vulnerabilities before malicious actors can. This skilled expert will collaborate with you to implement effective safeguards, ensuring your infrastructure remains safeguarded.
- Receive a comprehensive vulnerability assessment.
- Create tailored strategies to eliminate threats.
- Continue ahead of the curve in cyber security.
Don't wait until it's too late. Contact California's premier ethical hacker today and secure your online presence.
The State of Florida's Premier Hackers for Hire: Penetration Testing Specialists
Are you concerned about your digital defenses? In today's digitally-driven world, a strong system is crucial. That's where we team of expert penetration testers come in. We are Florida's|top-tier hackers for hire, dedicated to identifying vulnerabilities in your systems before attackers can exploit them.
Our team of skilled professionals utilizes cutting-edge techniques to simulate real-world attacks, providing you with a comprehensive evaluation of your security posture. This insightful information allows you to improve your defenses and protect your valuable data.
- Always wait for a breach to happen. Take a proactive approach to cybersecurity with our penetration testing services.
- Experts offer tailored solutions to meet your unique needs and limitations.
- Contact us today to discuss how we can help you obtain unrivaled cybersecurity.
Protecting Texas Businesses: Cybersecurity Expert Services
In today's constantly-shifting digital landscape, Texas businesses are confronted with a spectrum of cybersecurity threats. Remaining ahead of these dangers is essential to safeguarding sensitive data and securing business continuity. That's where specialized cybersecurity expert services come in.
Offering a wide selection of tools, these experts can help Texas businesses discover vulnerabilities, establish robust security measures, and remediate potential attacks. From data security to user training and incidentmanagement, cybersecurity experts provide the expertise needed to reduce risk and cultivate a secure digital environment.
A well-structured information security plan is critical for any Texas business, regardless of size or industry.
By utilizing the expertise of qualified cybersecurity professionals, businesses can strengthen their defenses and safeguard themselves against the evolving challenges of the digital world.
Elite Ethical Hackers: Upholding Digital Security
The realm of cybersecurity hinges on the expertise of top-tier ethical hackers. These digital warriors dedicate themselves to identifying and mitigating vulnerabilities within computer systems and networks before malicious actors can exploit them. Their comprehensive knowledge of hacking techniques, coupled with their unwavering commitment to ethical practices, makes them invaluable assets in the ongoing fight againstcybercrime.
Ethical hackers operate within established guidelines, always obtaining explicit permission from system owners before conducting penetration tests or security assessments. Their primary goal is to uncover weaknesses and provide actionable remediation strategies that strengthen defenses and protect sensitive data. By constantly pushing the boundaries of their expertise, they play a crucial role in shaping a more secure digital landscape for individuals, organizations, and nations alike.
Comprehensive Cybersecurity Evaluations: Leading Experts in Penetration Testing and Vulnerability Analysis
Securing your organization's digital assets requires a multi-layered approach. Implementing robust cybersecurity policies is crucial, but it's equally important to test those defenses regularly. Consider cybersecurity audits and red team exercises conducted by nationally recognized experts. These professionals possess the knowledge and experience to identify vulnerabilities, assess your security posture, and provide actionable recommendations to strengthen your defenses against increasingly sophisticated cyber threats.
- Network audits provide a comprehensive evaluation of your existing security controls, highlighting areas of weakness and compliance gaps.
- Red team exercises simulate real-world cyberattacks to test the effectiveness of your security measures and identify vulnerabilities before malicious actors can exploit them.
- Leading industry professionals bring a wealth of experience and specialized knowledge to ensure thorough and accurate assessments.
By leveraging the expertise of nationally recognized cybersecurity professionals, you can gain valuable insights into your organization's vulnerabilities Hackers and develop a more robust and resilient security posture.
 Jake Lloyd Then & Now!
Jake Lloyd Then & Now!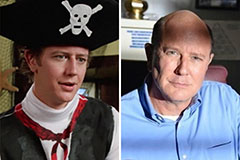 Judge Reinhold Then & Now!
Judge Reinhold Then & Now! Sydney Simpson Then & Now!
Sydney Simpson Then & Now! Mason Reese Then & Now!
Mason Reese Then & Now! Tina Louise Then & Now!
Tina Louise Then & Now!